Configure an identity provider
In its default configuration, Domino REST API uses itself as its identity provider (IdP), so it is client and IdP at the same time. This allows you to start evaluating and testing out of the box. To enable this, you need to have an HTTP password configured in Domino and good enough for internal use.
However, for an actual deployment, you might want to configure your own IdP and authentication flow. The only IdP requirements are use of a supported algorithm for signing and a token with the expected format.
Client Ids
When configuring an external identity provider using OpenID Connect (OIDC) or OIDC-idpcat with HCL Domino and the Domino REST API, you must specify a client ID. The default recommendation is to use Domino as the client ID for the Domino REST API server. However, your identity provider administrator might require a different value depending on your organization’s configuration.
Separate client IDs (application registrations) are required to support the Admin UI and Office Forms Based Authentication (OFBA). To support these features, configure at least the following clients in your identity provider:
- A client used by the Domino REST API server. You can name the client
Dominoor any descriptive name. The client secret might be managed throughidpcat.nsf. - A client used by the Domino REST API Admin UI. You can name the client
keepadminuior any descriptive name. Configure this client if you want administrators to authenticate through the external identity provider. - A client used for OFBA round-trip editing of Office documents. You can name the client
keepofbaor any descriptive name.
You should also create separate clients for each custom application that connects to the Domino REST API.
About this task
The provided information guides you of configuring your own IdP and authentication flow for use in an actual deployment.
Identity providers
Domino REST API supports identity providers that can produce JWT access tokens. Some examples are:
- Microsoft Active Directory
-
Redhat Keycloak
-
Tivoli Federate Identity Manager
- Okta
-
Auth0
Tip
Check out the Keycloak example configuration.
Example For Encode JWT
You can use the official JWT site to decode and inspect the encoded token.
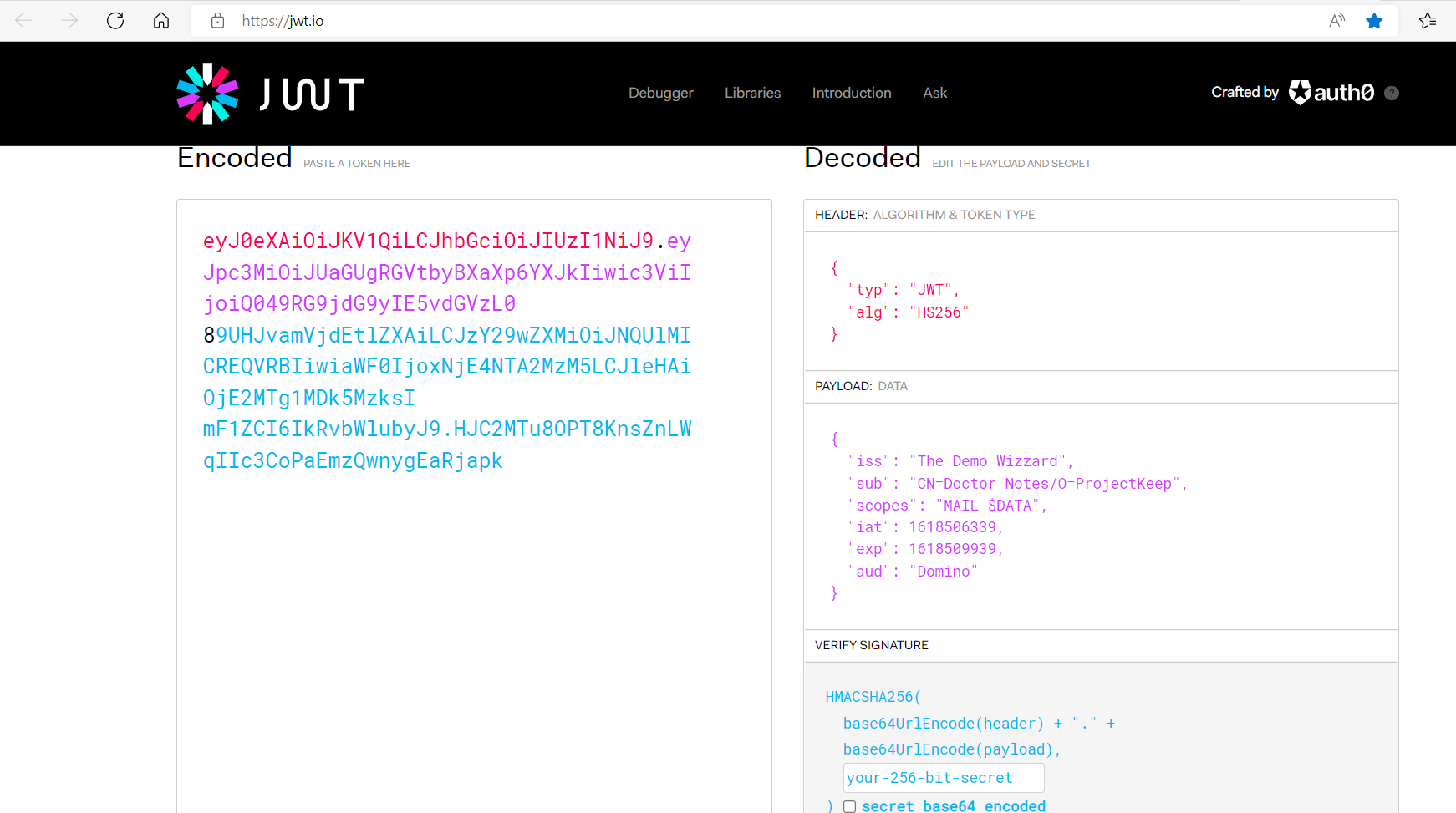
eyJ0eXAiOiJKV1QiLCJhbGciOiJIUzI1NiJ9.eyJpc3MiOiJUaGUgRGVtbyBXaXp6YXJkIiwic3ViIjoiQ049RG9jdG9yIE5vdGVzL0
89UHJvamVjdEtlZXAiLCJzY29wZXMiOiJNQUlMICREQVRBIiwiaWF0IjoxNjE4NTA2MzM5LCJleHAiOjE2MTg1MDk5MzksI
mF1ZCI6IkRvbWlubyJ9.HJC2MTu8OPT8KnsZnLWqIIc3CoPaEmzQwnygEaRjapk
When decoded, this translates to:
HEADER: ALGORITHM & TOKEN TYPE
{
"typ": "JWT",
"alg": "HS256"
}
PAYLOAD: DATA
{
"iss": "The Demo Wizzard",
"sub": "CN=Doctor Notes/O=ProjectKeep",
"scope": "MAIL $DATA",
"iat": 1618506339,
"exp": 1618509939,
"aud": "Domino"
}
wherein:
issstands for Issuer and refers to the name of the IdP providing the claim.substands for Subject and refers to the full qualified X500 expanded Notes name, which starts withCN=.-
scoperefers to the databases and services that the user accesses. For more information, see Scopes. -
iatstands for Issued at and refers to the epoch time of creation. expstands for Expiry and refers to the epoch time of expiration. It must fit intomaxJwtDurationnumber of minutes.audstands for Audience and MUST have a value ofDomino(case-sensitive).
VERIFY SIGNATURE
HMACSHA256(
base64UrlEncode(header) + "." +
base64UrlEncode(payload),
your-256-bit-secret
) secret base64 encoded
Add your own IdP
To add an IdP:
- Create a JSON file in the
keepconfig.ddirectory. - Allow access to the public key from your IdP.
The JSON file looks like this:
{
"disableJwtExpiryCheck": false,
"jwt": {
"my-idp": {
"active": true,
"algorithm": "RS256",
"keyFile": "10-jwt.pubkey"
}
}
}
wherein:
disableJwtExpiryCheck: By setting the value totrue, the enforcement of JWT expiration can be disabled. DO NOT do this on a production system (default isfalse).jwt: Entry is related to JWT authorization.my-idp: The name you give your IdP. It could beRumpelstielzchenbut needs to be unique on your server.active: True/false.algorithm: Currently supported:RS256.keyFile: Path to public key file (PEM format), either relative tokeepconfig.dor an absolute path.
Domino REST API supports more than one IdP, distinguished by the name my-idp in the example. Access checking takes longer the more identity providers you configure since Domino REST API checks every provider's key until it finds a match.
Obtaining the public key directly from the IdP
TO ease configuration and simplify key rollover, the public key for JWT verification can be directly obtained from the key server. You are responsible to only use trusted connections.
{
"disableJwtExpiryCheck": false,
"jwt": {
"somother": {
"active": true,
"providerUrl": "https://someidp.your.domain"
}
}
The Domino REST API will extend this URL to https://someidp.your.domain/.well-known/openid-configuration and check for a JSON return containing the jwks_uri key. When your IdP doesn't use the .well-known approach, such as Keycloak, you need to directly point to the key URL.
Note
Keycloak's providerUrl is different from the general IdP practice to use /.well-known/openid-configuration, mainly since Keycloak can handle multiple realms while the well-known approach cannot. Hence you need to use /auth/realms/[RealmName].